Imagine your email as a package traveling through a complex network of post offices. How do we ensure it’s not tampered with, comes from a legitimate sender, and arrives safely? That’s where our authentication protocols come into play.
Hey there! Today, we’re diving deep into the world of email authentication protocols. Buckle up, because we’re about to unravel the mysteries of DKIM, SPF, DMARC, and BIMI. These aren’t just random acronyms – they’re the unsung heroes keeping your inbox safe and your email deliverability on point.
Let’s start with DKIM, or DomainKeys Identified Mail. Think of DKIM as a wax seal on a medieval letter, but for the digital age.
Here’s how it works:
The sender’s email server adds a digital signature to the email header.
This signature is encrypted using a private key.
The receiving server uses a public key (published in the sender’s DNS records) to verify the signature.
DKIM uses asymmetric cryptography. The private key used for signing is typically 1024 or 2048 bits. The signature covers selected header fields and the message body, ensuring integrity of the content.
Next up is Sender Policy Framework (SPF). Imagine you’re throwing an exclusive party. SPF is like the bouncer checking the guest list.
SPF allows domain owners to specify which mail servers are authorized to send emails on behalf of their domain. Here’s the process:
The domain owner publishes SPF records in their DNS.
These records list IP addresses or hostnames of authorized sending servers.
Receiving mail servers check the sender’s IP against this list.
SPF records use specific syntax. For example:

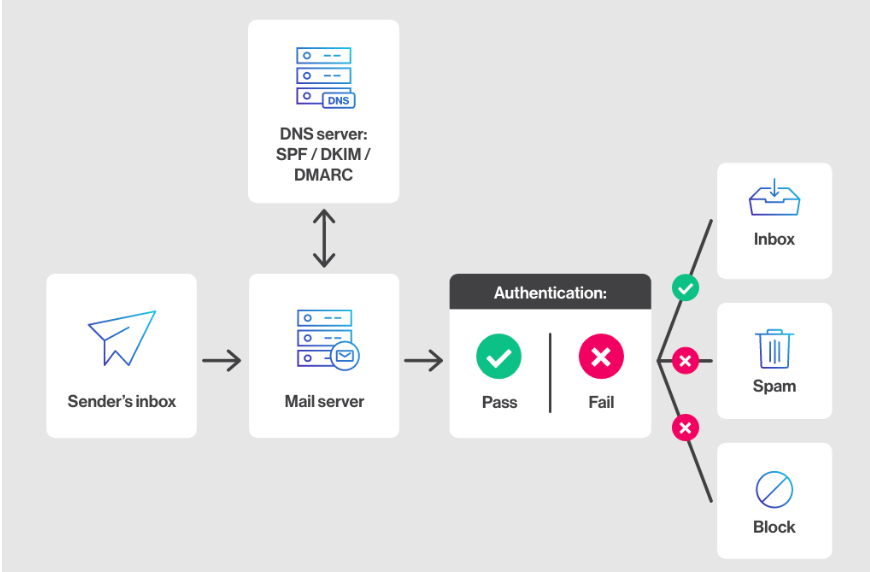
Now, let’s talk about DMARC (Domain-based Message Authentication, Reporting, and Conformance). If DKIM and SPF are the bouncers, DMARC is the club owner setting the rules.
DMARC does three crucial things:
Tells receiving servers what to do if an email fails DKIM or SPF checks.
Specifies how to handle alignment between the “From” address and the authenticated domain.
Provides a reporting mechanism for domain owners.
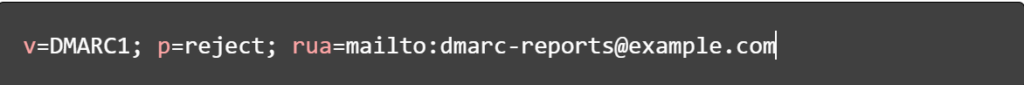
A DMARC record looks something like this:
Last but not least, we have Brand Indicators for Message Identification (BIMI). Think of BIMI as the VIP pass that comes with a fancy logo.
BIMI allows domain owners to specify a logo that email clients can display alongside authenticated emails. Here’s the kicker – it only works if you’ve properly implemented DKIM, SPF, and DMARC.
BIMI requires a VMC (Verified Mark Certificate) from an authorized provider.
These protocols work in harmony to create a robust email authentication system:
DKIM ensures the email hasn’t been tampered with.
SPF verifies the sender is authorized.
DMARC sets the policy and provides feedback.
BIMI rewards good actors with brand visibility.
Together, they significantly reduce email spoofing and phishing and improve deliverability.
And there you have it, folks! The intricate world of email authentication protocols is demystified. Remember, implementing these protocols isn’t just about security – it’s about maintaining trust in email communications.
share this article :

Optimizing your checkout process is one of the most effective and straightforward strategies for enhancing your conversion rates.

Selecting the optimal paid advertising platform is crucial for maximizing your e-commerce venture's potential and ...
Imagine your email as a package traveling through a complex network of post offices. How do we ensure it’s not tampered with, comes from a legitimate sender, and arrives safely? That’s where our authentication protocols come into play.
Hey there! Today, we’re diving deep into the world of email authentication protocols. Buckle up, because we’re about to unravel the mysteries of DKIM, SPF, DMARC, and BIMI. These aren’t just random acronyms – they’re the unsung heroes keeping your inbox safe and your email deliverability on point.
Let’s start with DKIM, or DomainKeys Identified Mail. Think of DKIM as a wax seal on a medieval letter, but for the digital age.
Here’s how it works:
The sender’s email server adds a digital signature to the email header.
This signature is encrypted using a private key.
The receiving server uses a public key (published in the sender’s DNS records) to verify the signature.
DKIM uses asymmetric cryptography. The private key used for signing is typically 1024 or 2048 bits. The signature covers selected header fields and the message body, ensuring integrity of the content.
Next up is Sender Policy Framework (SPF). Imagine you’re throwing an exclusive party. SPF is like the bouncer checking the guest list.
SPF allows domain owners to specify which mail servers are authorized to send emails on behalf of their domain. Here’s the process:
The domain owner publishes SPF records in their DNS.
These records list IP addresses or hostnames of authorized sending servers.
Receiving mail servers check the sender’s IP against this list.
SPF records use specific syntax.
For example:

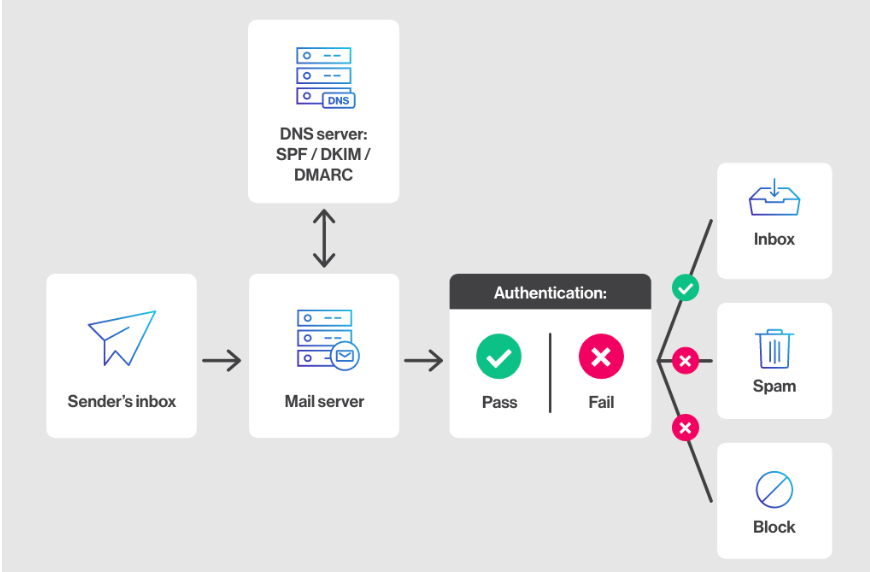
Now, let’s talk about DMARC (Domain-based Message Authentication, Reporting, and Conformance). If DKIM and SPF are the bouncers, DMARC is the club owner setting the rules.
DMARC does three crucial things:
Tells receiving servers what to do if an email fails DKIM or SPF checks.
Specifies how to handle alignment between the “From” address and the authenticated domain.
Provides a reporting mechanism for domain owners.
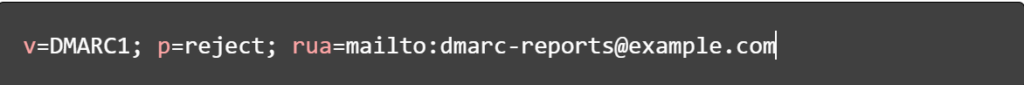
A DMARC record looks something like this:
Last but not least, we have Brand Indicators for Message Identification (BIMI). Think of BIMI as the VIP pass that comes with a fancy logo.
BIMI allows domain owners to specify a logo that email clients can display alongside authenticated emails. Here’s the kicker – it only works if you’ve properly implemented DKIM, SPF, and DMARC.
BIMI requires a VMC (Verified Mark Certificate) from an authorized provider.
These protocols work in harmony to create a robust email authentication system:
DKIM ensures the email hasn’t been tampered with.
SPF verifies the sender is authorized.
DMARC sets the policy and provides feedback.
BIMI rewards good actors with brand visibility.
Together, they significantly reduce email spoofing and phishing and improve deliverability.
And there you have it, folks! The intricate world of email authentication protocols is demystified. Remember, implementing these protocols isn’t just about security – it’s about maintaining trust in email communications.
share this article :

Optimizing your checkout process is one of the most effective and straightforward strategies for enhancing your conversion rates.

Selecting the optimal paid advertising platform is crucial for maximizing your e-commerce venture's potential and ...